ファイルレス攻撃が増加
ファイルレスマルウェアを防止
ファイルレスマルウェアは、正規のプログラムを使用してシステムに感染するため、足跡が残らず、EDRのような検知·対処型のツールでは感染を拡大させる前に感染を止めることが困難です。Deep Instinct は、ファイルレスマルウェアの DNA を理解し、検知回避のために進化し、発見が困難な脅威であっても、攻撃を防止します。
Living off the Land 攻撃を
させない
Living off the Land 攻撃は、マルウェアがディスクに書き込まれず、アーティファクトを残さないことから、ファイルレスに分類されます。Deep Instinct は、疑わしい異常動作を理解することで、攻撃が実行される前にこれらの攻撃を防止します。
ディープラーニングの優位性
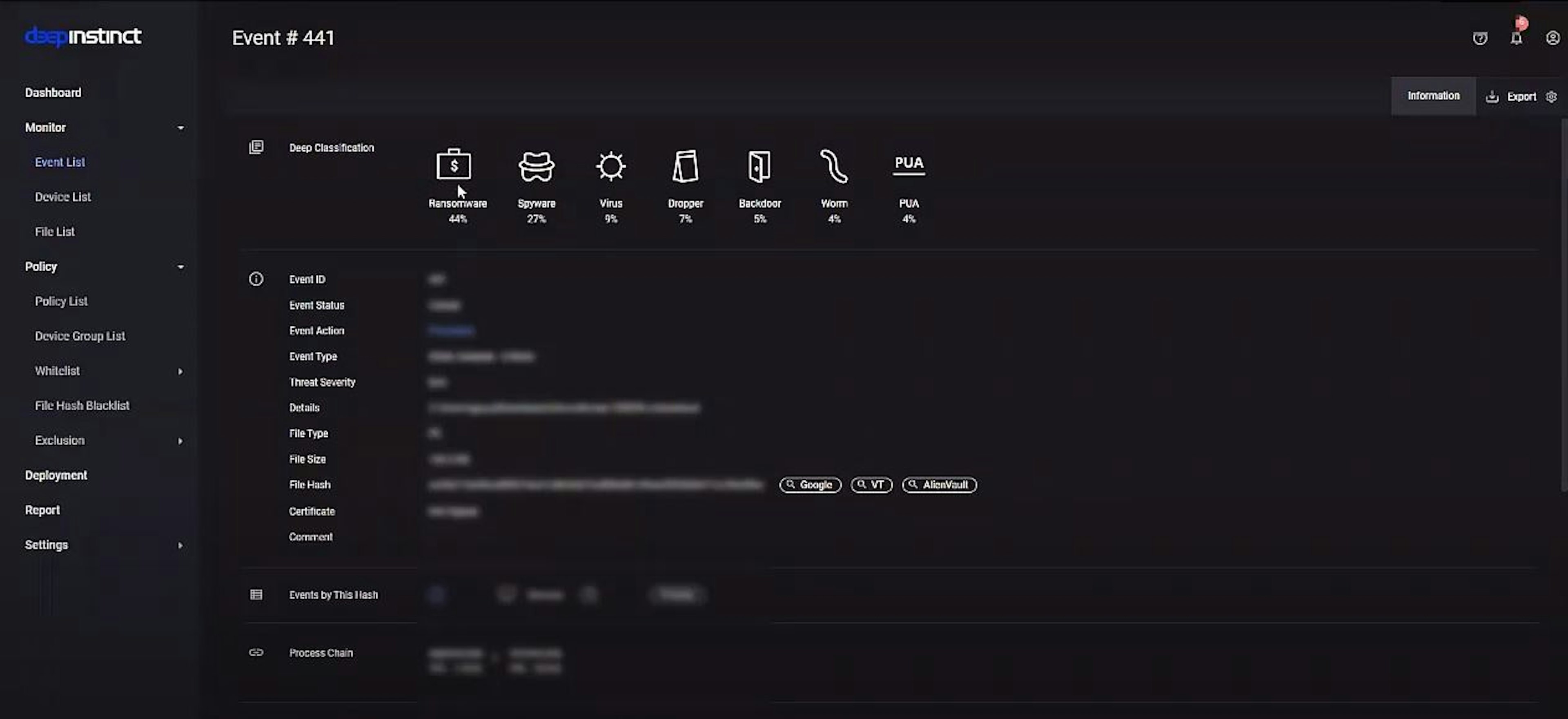
未知のランサムウェア攻撃を 99% 阻止
ファイルレス攻撃は、シグネチャベースの従来型ツールでは検知が困難です。サンドボックスで判断が遅すぎますし、機械学習ベースの製品では実行ファイルが見えないファイルレス攻撃を防ぐのには不十分です。Deep Instinct の独自のディープラーニング アプローチは、ファイルレス攻撃の DNA を理解し、被害が発生する前に攻撃を停止させます。
シェルコードを止める
悪意ある PowerShell スクリプトから保護
PowerShell スクリプトは、アプリケーションに埋め込まれた悪意のあるコードを利用して攻撃者のペイロードを実行し、シェルコード攻撃を開始するために使用されます。また、スクリプトは検知を回避するために使用されることが多く、攻撃者は感染後に横方向に移動することができます。Deep Instinct は、悪意あるシェルコードを識別し、即座に実行をブロックすることで、これらの脅威を防止します。
予防力を上げて、誤検知を減らす
よく使われるメモリ常駐型の攻撃を阻止
メモリベースの攻撃 は、最も頻繁に使用される高度なエクスプロイトです。インメモリ攻撃に対しては、既知のシグネチャや実行コードのパターンマッチングでは検知ができにくい上に、多くの誤検知を引き起こします。ディスク上で実行されるファイルに依存する基本的なマルウェア対策ツールでは、こうした脅威を防ぐことはできません。Deep Instinct は、悪意あるコードをメモリ内で特定し、被害が発生する前に攻撃を阻止します。
サイバー攻撃は 39 秒に 1 回発生しています*。
*出典: メリーランド大学クラーク校が実施した調査により、コンピュータは 1 日平均 2,244 回ハッキングされていることが判明。この調査で、39 秒に 1 台のコンピュータがサイバー犯罪者に攻撃されていることが確認された。
反射型 DLL インジェクション
リモートコードインジェクション攻撃を回避
反射型 DLL インジェクションのようなリモートコードインジェクション攻撃は、悪意のあるダイナミックリンクライブラリ(DLL)をディスクではなくメモリからロードするものです。洗練された攻撃者は、この手法の従来の検知を回避することができるようになりました。Deep Instinct は、リフレクティブ DLL インジェクションを特定し、システムが侵害される前にその実行を停止させることができます。