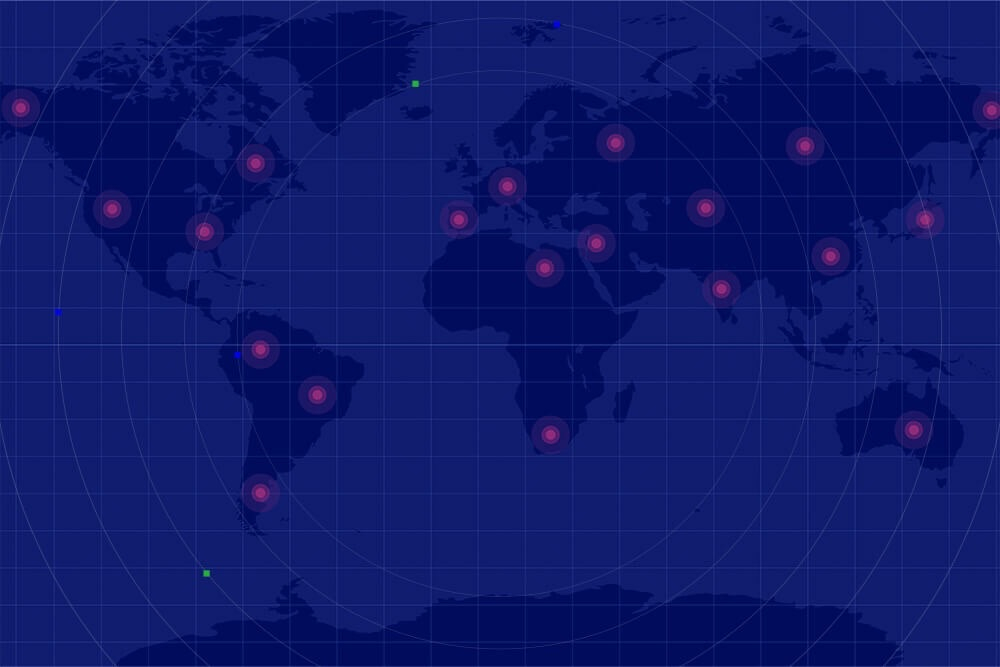
2021 Mid-Year Cyber Threat Landscape Report
It’s usual at Deep Instinct to compile an annual Threat Report. However, this year has been exceptional for cyber threats, and as a result, we decided to create an interim version taking into consideration the last six months and our key observations. While shorter, many of the sections are consistent with the full-year report.
In “Malware trends,” we explore an extended period (January 2020 through June 2021), and the arbitrary amount of new samples across malware campaigns such as Miner, Dropper, Spyware, Worm, and Backdoor. Unsurprisingly, ransomware is still the dominant trend.
Ransomware has been a featured in major news headlines throughout 2021, and our “Ransomware campaigns” sections looks at the five leading threats such as STOP (Djvu), Ryuk, and Sodinokibi (REvil), which has been featured in many recent high-profile attacks. We dive into the key attributes of these and provide some wider context where possible.
“Banking Trojan campaigns” looks at the successors to Emotet, such as Ramnit, Qbot, and IcedID. These and other campaigns have all had a significant impact on financial services and eCommerce, as these sectors battle with online banking fraud. We are also seeing the Dridex campaign enabling even cryptocurrency wallet credential theft – no matter what the currency or its format, every one of these is fair game for threat actors.
“Takeaways” focuses on our key observations on the first six months of 2021. The global pandemic has sadly given cyber criminals multiple opportunities to exploit technology and human vulnerabilities. From phishing emails disguised as Pfizer, to healthcare institutions being specifically targeted, and the exploring of back doors in hastily developed COVID vaccination applications, the pandemic has gifted hackers with multiple opportunities to make the most of an extraordinary situation.
Looking ahead to the rest of 2021, “Predictions” is always a topic of enthusiastic debate on our team, as we consider how the cyber threat landscape is likely to evolve. A key expectation we have is around the long-term implications of employees working from home, whether permanently or in a hybrid model. The absence of the classic perimeter within an office-based environment is a major game changer for the cybersecurity industry.
The Colonial Pipeline attack made worldwide news, but it is just one of many attempts to hit mission-critical infrastructure, whether law enforcement, hospitals, education, or the energy and utility sectors. We do not expect to see this potentially lucrative and high-profile strategy changing anytime soon, and it forms one of our other major predictions.
Want to know more about our findings? Download the report and read the full analysis.