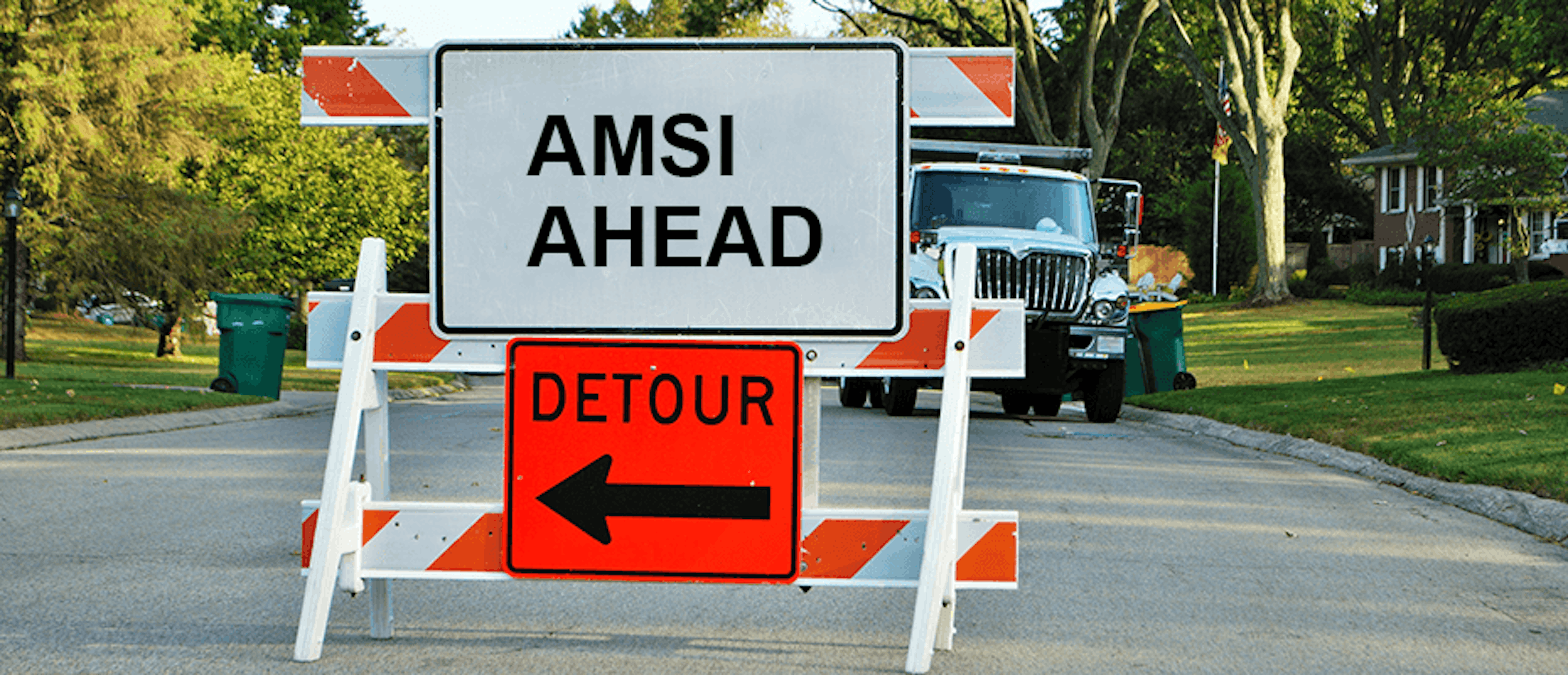
AMSI Unchained: How to Unchain the Antimalware Providers and Bypass AMSI
The Deep Instinct Research team has found two new AMSI bypass techniques; read the white paper.
AMSI (Anti-Malware Scan Interface) is Microsoft’s framework that allows third-party antimalware solutions to gain visibility into Microsoft components and applications, such as PowerShell, script engines, .NET framework, and WMI. Endpoint Detection and Response (EDR) solutions use this framework to scan files, memory, and/or streams for malicious payloads.
Bad actors responded to these defensive approaches by developing multiple AMSI bypass techniques. This started an innovation battle between the attackers and EDR solutions, who have tried to play keep-up and protect their customers against these threats. There was initially an explosion in new bypass techniques but efforts on both sides have reached stagnation, with the last AMSI bypass technique being introduced back in 2019.
To address these threats, Deep Instinct mapped all known AMSI bypass techniques and developed complete protection against them. During these efforts our researchers found two new portable, undocumented, and undetected AMSI bypass techniques that target an unmonitored area of the AMSI architecture.
After full disclosure to Microsoft and a subsequent presentation at Black Hat ASIA 2022, we wrote a white paper that details these findings in-depth – we'd welcome you to read the full research white paper and discover how AMSI bypass attacks have become stealthier than ever. Or, if you’d prefer, request a demo.