Blog
Perspective & Findings
As our experts uncover critical finders, we find it only necessary to keep you informed. From perspective on recent threats to best practices in security we cover it.
Featured Blog Post
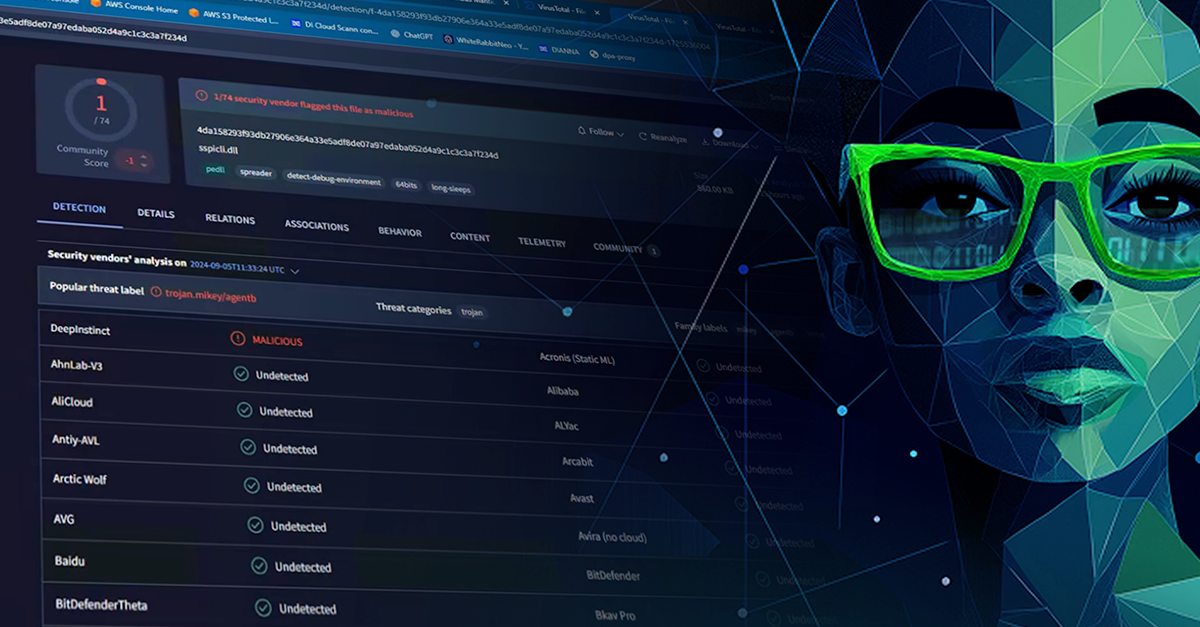
How a Guardrail-Free LLM Outsmarted Legacy Cyber Tools
A black hat hacker’s experiment with an unrestricted AI exposed how vulnerable legacy cyber tools are to fast-evolving, AI-generated threats.
Recent Blog Posts
Schrödinger’s Cloud: Both Safe and Compromised
January 21, 2026
Overconfident and Underprepared: IT Leaders Misjudge AI Cyber Risk
December 10, 2025
DIANNA Explains 4: Nimbus Manticore—Monstrous Malware
December 3, 2025