Highly Evasive Formbook Campaign Targets Victims Globally
Formbook is a long-lived information stealer, which has been around for several years. We have also published about it in the past. A recent attack wave of Formbook was recently prevented by Deep Instinct in one of its customer sites. This wave appears to target victims globally. The attack begins with a malicious PDF dropper, which then drops an Office document, which in turn downloads the final Formbook payload.
Initial analysis of this PDF document aroused our suspicion, as it seems to exploit CVE-2017-11882, a known MS-Office equation editor vulnerability exploited often in Office and RTF documents. Upon further investigation, we found the PDF dropper employs an interesting infection chain, involving an Office file, which ends in the dropping and execution of the Formbook information stealer.
Infection flow
General flow:

The infection flow starts with the victim receiving an email with a PDF attachment. The email subject is a standard quotation request, so the malicious PDF file tries to trick the victim by being named “REQUEST FOR QUOTE.pdf”. Based on the email recipient and Deep Instinct production telemetry, it appears this attack wave is targeting victims all around the globe.
Once the PDF is downloaded and executed, it runs an OpenAction event which leads to the user being presented with a decoy message, and a warning window, which asks the user if the file “is secured and verified however docx, PDF,.xlam” should be opened.
[caption id="attachment_6520" align="alignnone" width="923"]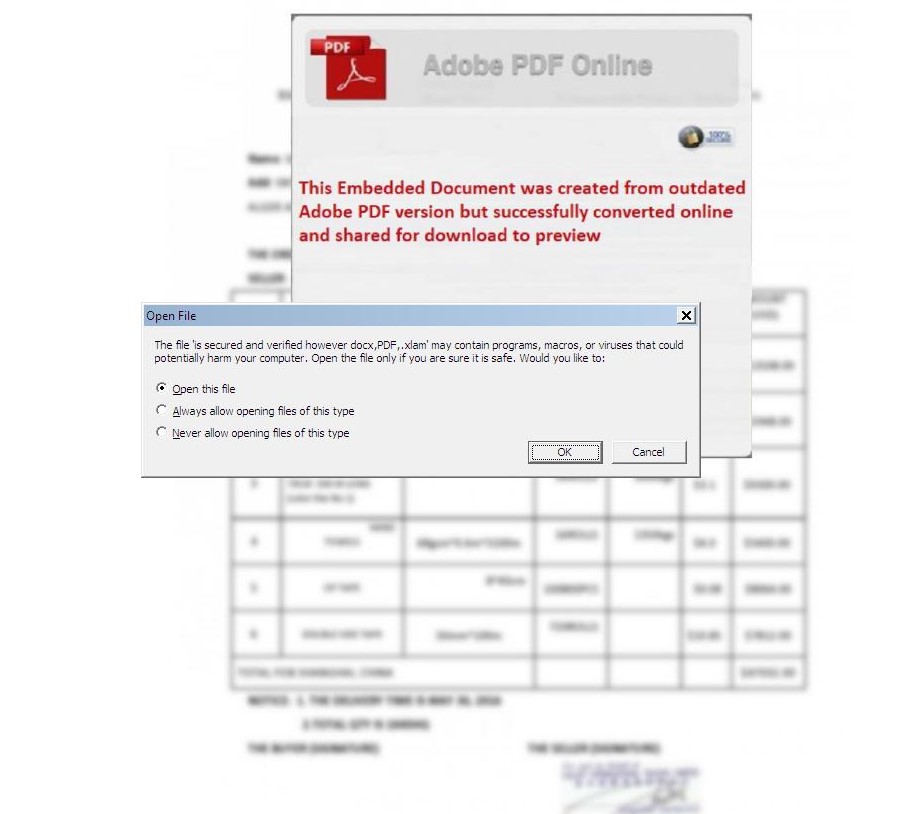 The warning that is shown to the user when the PDF document attempts to open the embedded XLAM document[/caption]
The warning that is shown to the user when the PDF document attempts to open the embedded XLAM document[/caption]
If the user opens the file, an XLAM (an Excel Macro-Enabled Add-In) document, which is embedded in the PDF, is executed. This document exploits CVE-2017-11882 to download the Formbook payload through svchost.exe. The document attempts to download the Formbook payload from hxxp://challengerevertprocessupdate.duckdns.org/office/vbc.exe. The PE payload has a PDF icon, to fool unsophisticated users.
Once the Formbook payload is downloaded, it performs the following actions, which are similar to previous Formbook campaigns:
- Attempts to harvest and steal browser and mail credentials
- Takes screenshots
- Attempts to contact and post data to C2 servers (IOCs provided later)
- Persists through an AutoStart registry key
The payload is signed with an invalid X509 certificate belonging to CyberLink Corp, which is a large multimedia software company located in Taiwan. Since the signature is invalid, it appears the attempts of the attacker to distribute this file as a signed CyberLink file were unsuccessful.
Evasion techniques
In this new attack wave, Formbook deploys several evasion and anti-analysis techniques, which complicate the analysis of each stage in the infection flow. Initially, the PDF file can’t be analyzed with regular PDF static analysis tools, such as Peepdf or pdftk, as both tools crash when trying to parse the file, probably due to mishandling of specific objects inside the malicious PDF file. In addition, the XLAM document arrives encrypted which complicates analysis with Office static analysis tools, such as oletools. However, the XLAM file is decrypted on execution and can be analyzed dynamically. XLAM is also a rarely used format, so it might not be blocked by certain network security products.
In addition, the final PE payload is written in .NET, and the .NET code of the file is highly obfuscated.
[caption id="attachment_6518" align="alignnone" width="879"]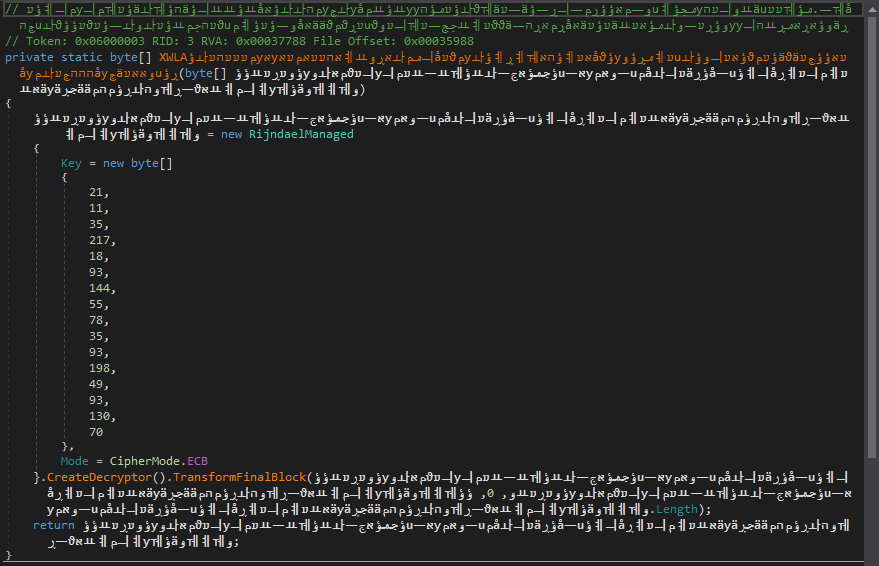 The obfuscated segment of the .NET PE payload[/caption]
The obfuscated segment of the .NET PE payload[/caption]
In this case, as well, the file can be analyzed dynamically without difficulty. It should be noted that encrypted or obfuscated Formbook samples written in .NET were also seen in previous attack waves of Formbook.
The malware also includes some additional evasion techniques, such as a long sleep (several minutes) and several methods to detect virtualization.
Refusing to be Characterized
Attackers constantly evolve in order to try and evade security solutions and complicate the analysis of their malware. The complex execution flow of this Formbook attack is another innovative attempt by attackers to evade detection. In addition, the anti-analysis techniques incorporated in all files used in the infection flow are an attempt by attackers to make the characterization of the attack more difficult.
Deep Instinct’s customers are protected from this new attack wave of Formbook, which we prevent at the earliest possible stage.
IOCs
Analyzed samples
PDF dropper: 520b9c0c81cd34a95c0439f8ed3addd5e39aed22de4798fb3ab9173f7fe251b1
XLAM dropper: e66786bb4fb9ec568a86c51a060284197f2342f09fd1a6568751d1570d9b36ee
PE payload: c7722bb0e745b981dc978a624139cf0cd6920a230c20ea552dfbd1a41be37849
PE X-509 SHA1 thumbprint: c55a46f6b27c446e4a6e74cfc7b376d18389d2b8
Additional PDF droppers
af506c21aa740d0c978b920482f7cc4409592b30012ab3e66306c8866170ec34
91dd44d0e6ba45f7b5e5ae3a1fa104549f9220e4ee74b061c2c952bb552de08b
94ef08bfc650da4e4122432cf834f0a29be49b9ca05da0fa3ce074718f50db95
367912cc8ffd6db400090b1febd6b9ac6ec8eb8fa3b864ef2671d3074a53b821
19c04a3aa7862294f2ca566ee2ae37a0ad2cb410f6fab7bb762dbff985e7cfd9
520b9c0c81cd34a95c0439f8ed3addd5e39aed22de4798fb3ab9173f7fe251b1
98f4e7ed6333bbc48277880d2f3d6c23770cde9a7a3c0ddda92be60e6ca50165
87e421a1cfd5c98b9d0924ae5a48ec16b3650706b7580821fe013a6a505e7e3a
f6a8ef3d8e2bb663b2badbddeecb61f53a5b4aa0830d0cbb8e75bc22b5d952e6
5622caf6fff3d0cc6bff94812d42be49faa45a717445031d5cdfe63fd7bf3fba
387b19e579ff7130eb0154f74143ffc4ba66ff0a383c146c5f2c23a4ec172a41
c50e75f491c8bc525e41eb714440bb62dc4b46160ba38b9ed7d051d99499a89b
f4e33529d9aafbc00c0e1fef2c52892ed89a7ec32903ba0465023e7fbcd9a490
901b45b0897691db2f549a315fb12334d62f3ecff077adb3efd61defa241876c
80983238f2fa79d0938f63f241d0ebb8a98d1ffcc4b76e58f44d778e4c8bd6a0
f76dd2d60095b1880b1bd022cd28a39ed3700bacf4cdb90381461a5e50e55236
Network Indicators
hxxp://challengerevertprocessupdate.duckdns.org/office/vbc.exe
hxxp://sindomac.com/lc/

